VPN is becoming increasingly popular today. And perhaps you’ve probably heard of the term “VPN Tunnel”. But what is it exactly? And what does it have to do with VPN?
What is VPN tunnel?
In normal cases, your computer or device is connected to the Internet directly. All your data is transferred directly between you and the Internet.
But this is not the case when using a VPN (virtual private network) connection. Your computer or device is connected to the Internet through the VPN. And your data (in and out) will be routed through that network.
And the connection between your device and the VPN is called the tunnel. However, the tunnel is not secured unless it is encrypted with a proper method. And the method being used depends on what type of VPN tunneling protocol you’re using.
What are the common types of VPN tunneling protocol?
There are several commonly used protocols to encrypt VPN tunnels. And they have different characteristics and security levels. You’ll be able to configure them when setting up your VPN connection. But you may need to know a bit more about them beforehand.
1. PPTP
Point-to-Point Tunneling Protocol (PPTP) is the one of the oldest and least secure tunneling protocol. It’s a fast protocol and compatible with older devices. This protocol is easy to set up, so you may consider it in the situation where you don’t need a high level of security.
2. L2TP
Layer 2 Tunneling Protocol (L2TP) is a more secure protocol than the PPTP. It doesn’t have the ability for encryption on its own. So it is usually used with a protocol called Internet Protocol Security (IPsec) to encrypt and encapsulate the communication.
3. SSTP
Secure Socket Tunneling Protocol (SSTP) is a protocol developed by Microsoft and mainly used in its Windows system (Windows Vista SP1 or later). It transfers your data using Secure Sockets Layer (SSL), a widely used encryption protocol on the Internet.
4. IKEv2
Internet Key Exchange, Version 2 (IKEv2) is a protocol developed by Microsoft with Cisco. It’s fast, and allows you to easily re-establish your VPN connection if it was broken. It does not support the older authentication methods that has lower level of security.
5. OpenVPN
OpenVPN is an open source protocol. That means if there are any vulnerabilities, it will be easily and quickly identified by its open community. It is considered one of the most secure protocols. Also, the OpenVPN protocol is compatible with various operating systems and platforms, and it’s used in multiple popular VPN services.
Which type of VPN tunneling protocol should I use?
We don’t recommend you use PPTP and L2TP because they are a bit outdated and less secure, compared to the others.
On the other hand, OpenVPN, as a popular and secure option, may satisfy your need. If your device or VPN service doesn’t support this protocol, SSTP and IKEv2 are also recommended options for you.
Are there any VPN service that supports these protocols?
There are a lot of VPN services supporting the IKEv2 and OpenVPN protocols. We would recommend using NordVPN. NordVPN helps you set up a fast, stable and secure Internet connection to anywhere. And it helps you do this with just a few clicks!
To use NordVPN:
- Download and install NordVPN.
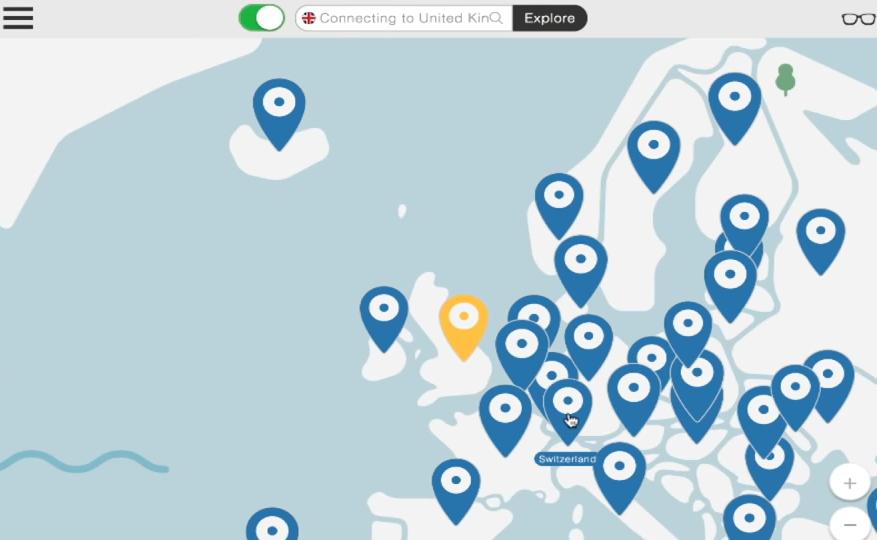
- Run NordVPN, then choose a location you want to connect to.
That’s it! You’ve already set up a VPN connection to the Internet on your computer!