Don’t know how to spot phishing emails and avoid phishing scams? Don’t worry! You’ve come to the right place. In this post, we’re going to show you some useful tips on how to protect yourself from phishing emails.
What is phishing?
As is the simplest sort of online scam, phishing is typically carried out by cyber-criminals through unsolicited email and / or websites that appear to be from a legitimate company or organization. Scammers often launch phishing attacks to con users into providing their personal information, such as username, credit card number, password and more.
How does a phishing email attack work?
To perform a phishing email attack, the scammer often cunningly disguises himself as the official person from the government, a legitimate organization or company. Once you open the phishing email and if you don’t carefully analyze it, there’s a big chance that you’ll take the bait and click the link in that phishing email.
Just like the phishing email, the web page that the suspicious link in the email points to also looks almost identical to the official website. If you enter your personal information on that web page, you’re providing your sensitive information to the cyber criminal.
Sometimes, the suspicious links in the phishing email don’t point to a website. Instead, once you click on it, it will implant a Trojan virus into your computer. Once the Trojan virus is in your computer, the personal information on your PC is at the cyber-criminal’s fingertips.
How to recognize phishing?
Here’re some signs of a phishing email:
The email contains grammar or spelling mistakes
The emails from a legitimate company or organization should be well-written. If the email claims that it’s from a big organization or company but it contains typos or grammar errors, this may be a phishing email.
The email doesn’t not call you by your name
Legitimate companies usually call you by your name. If a company requires your account information, the email would call you by your name. If the Email doesn’t call you by your name, instead, it uses generic salutations like “Dear customer”, “Dear account holder “, “Dear user”, “Dear valued member”, it may be a phishing email.
The email address is different from the official one
A big or famous company has its domain emails. If you notice the email address is different from the official one, you need to pay attention. Cyber-criminals always use an email address that looks very similar to the official one.
Other tips on recognizing phishing email
If you receive any emails that
- offer coupons for free stuff.
- say you must confirm some sensitive information.
- claim there’s a problem with your account or your payment information.
- lure you to click on a link to make a payment.
- say they’ve noticed some suspicious activity or log-in attempts on your social network accounts.
- say they’re from XX bank and ask for your PIN and password.
Please be alert and DO NOT CLICK no any links in those emails.
How to avoid phishing scams?
To avoid phishing scams and protect yourself from phishing emails, the first thing you should bear in mind is “DO NOT CLICK on any suspicious links in emails”.
Besides, you should protect your computer by using the security software and set it to update automatically so that it can handle with any new cyber-attacks. If you don’t know which security software you can trust, you can choose the one you like from the following:
1. AVG Antivirus Free
AVG Antivirus is one of the most famous antivirus software across the globe. With the Web Shield and the Email Shield features, AVG Antivirus Free protects you from the phishing scams when you surf the internet and check the emails.
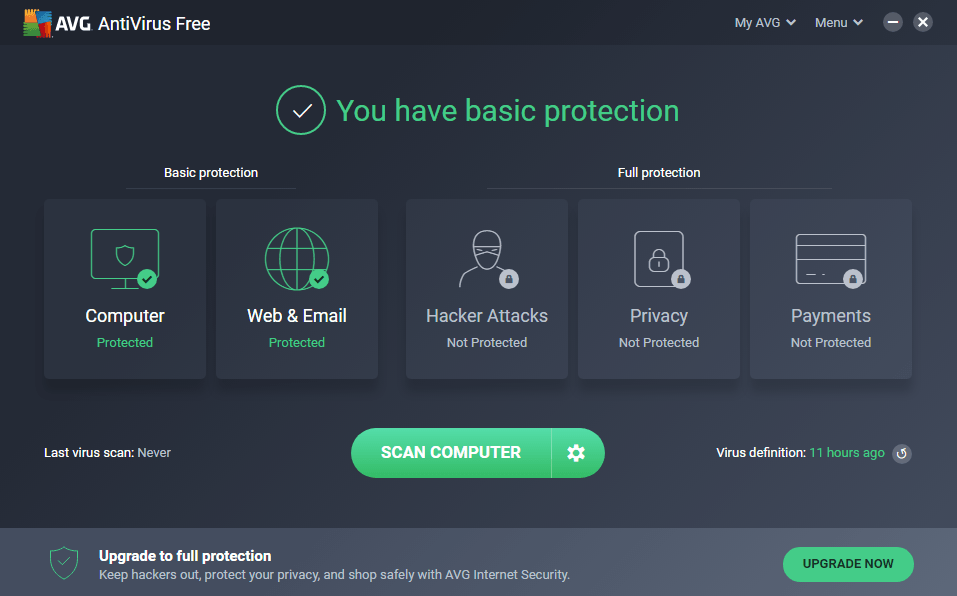
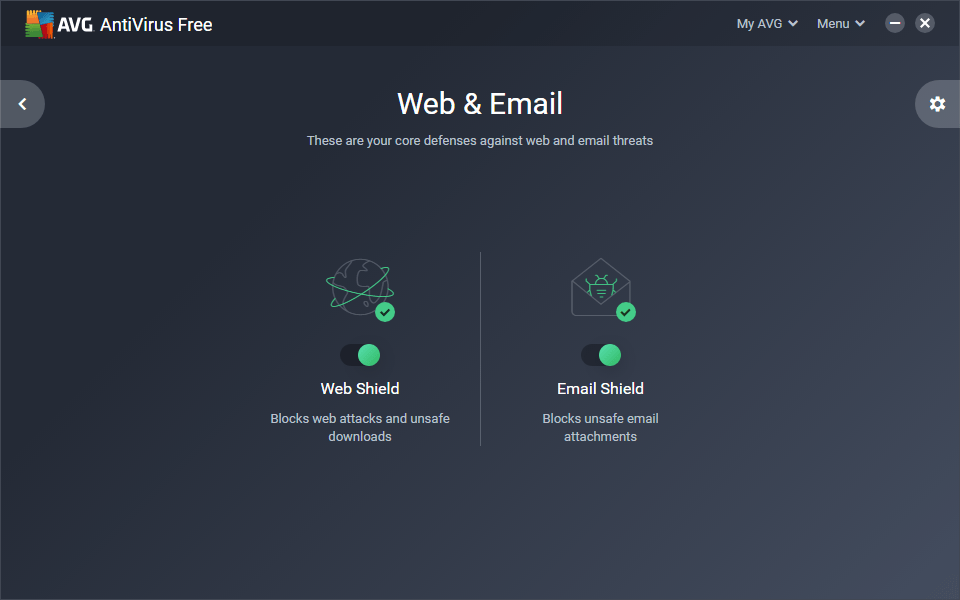
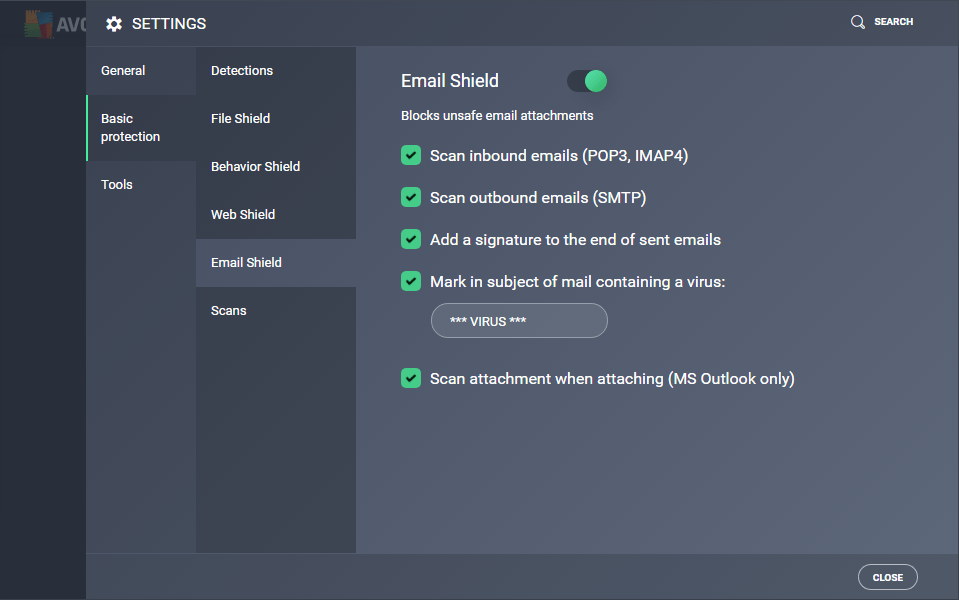
Want to give it a try? Just download and install it on your PC.
2. Norton Security
Norton Security is another popular antivirus software around the world. The Safe Web / Antiphishing feature in Norton Security helps you avoid the phishing scams automatically. What’s more, in the AntiSpam settings, you can customize the Allowed List and the Blocked List of your email.
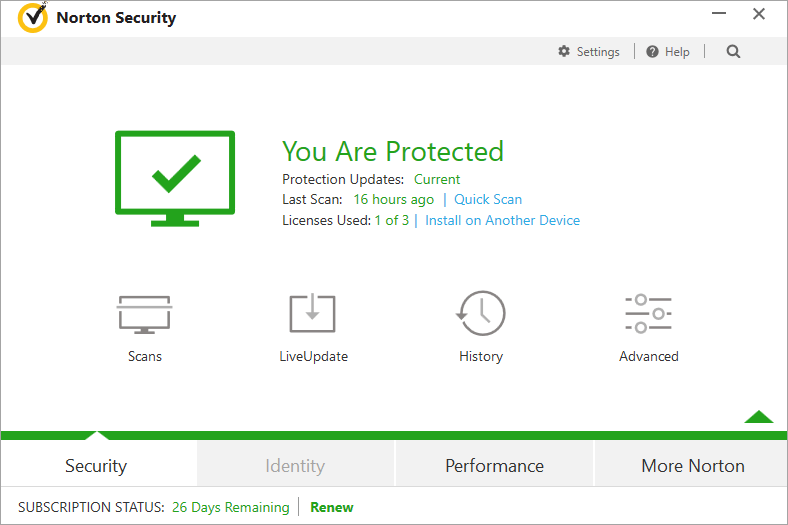
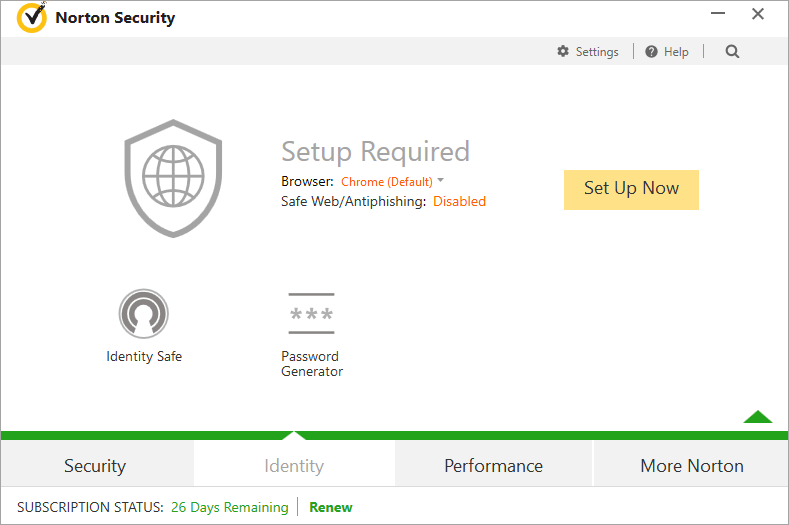
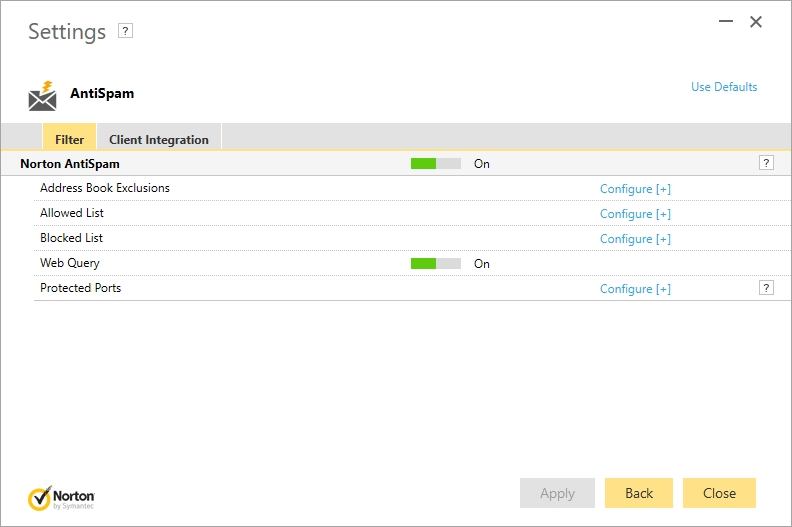
Norton Security offers a 30-day trial. If you want to give it a shot, you can see Norton Download and Install!
Hopefully you find this post helpful. If you have any questions, ideas or suggestions, you’re more than welcome to leave a comment below.